Monitoring Documentation About 45.76.33 and Activity Logs
Monitoring documentation concerning the IP address 45.76.33 is crucial for organizations focused on network security. By scrutinizing associated activity logs, entities can uncover patterns in user behavior and identify potential security breaches. The structured nature of these logs aids in recognizing trends and anomalies. However, the effectiveness of monitoring hinges on the implementation of best practices and retention policies. What strategies can organizations adopt to enhance their cybersecurity posture effectively?
Understanding the Significance of Monitoring IP Addresses
Monitoring IP addresses is a critical component of network security and management, as it provides valuable insights into the behavior of users and devices within a system.
IP address tracking enables organizations to identify unauthorized access, detect anomalies, and analyze traffic patterns. This proactive approach not only enhances network security but also promotes a transparent and accountable digital environment, fostering the freedom users seek in their online interactions.
Key Components of Activity Logs
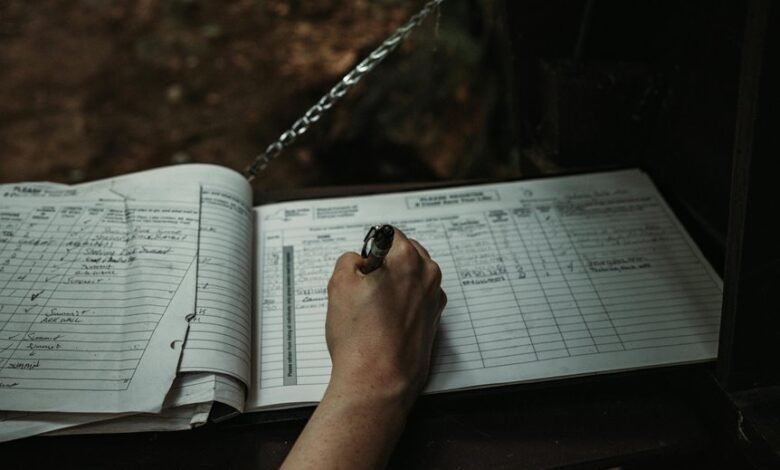
Activity logs serve as a foundational element in the broader framework of network management and security, complementing efforts to monitor IP addresses.
Key components include standardized log formats that facilitate consistent data presentation and ease of analysis.
Moreover, effective data retention policies ensure that logs are preserved for relevant durations, enabling thorough investigations and audits while maintaining compliance with regulatory requirements.
Best Practices for Analyzing Activity Logs
Analyzing activity logs requires a systematic approach to ensure that critical insights are derived effectively.
Best practices include employing log analysis techniques to identify trends and anomalies, while utilizing data visualization tools to present findings clearly.
Prioritizing the categorization of log data enhances interpretability, enabling stakeholders to make informed decisions.
Regular review cycles further ensure that the analysis remains relevant and actionable.
Enhancing Cybersecurity Through Effective Monitoring
While organizations increasingly face sophisticated cyber threats, effective monitoring serves as a critical component of a comprehensive cybersecurity strategy.
It enhances threat detection capabilities, enabling swift identification of vulnerabilities. Additionally, structured monitoring facilitates timely incident response, ensuring that organizations can mitigate risks and protect sensitive information.
Ultimately, a proactive approach to monitoring empowers organizations to maintain their operational freedom while safeguarding against evolving cyber threats.
Conclusion
In conclusion, the meticulous monitoring of the IP address 45.76.33 and its activity logs reveals a dual purpose: safeguarding network integrity while simultaneously uncovering patterns that may predict future threats. Coincidentally, as organizations refine their retention policies, they not only bolster compliance but also enhance their ability to respond swiftly to incidents. Thus, the synergy between detailed log analysis and proactive cybersecurity measures fosters a resilient network environment, ultimately transforming potential vulnerabilities into strengths.







